and Software

 Location & Weather API
Identify Your
Location & Weather API
Identify YourField on a Map
 Nutrients Calculation
Upload Tests
Nutrients Calculation
Upload TestsFrom Your Field
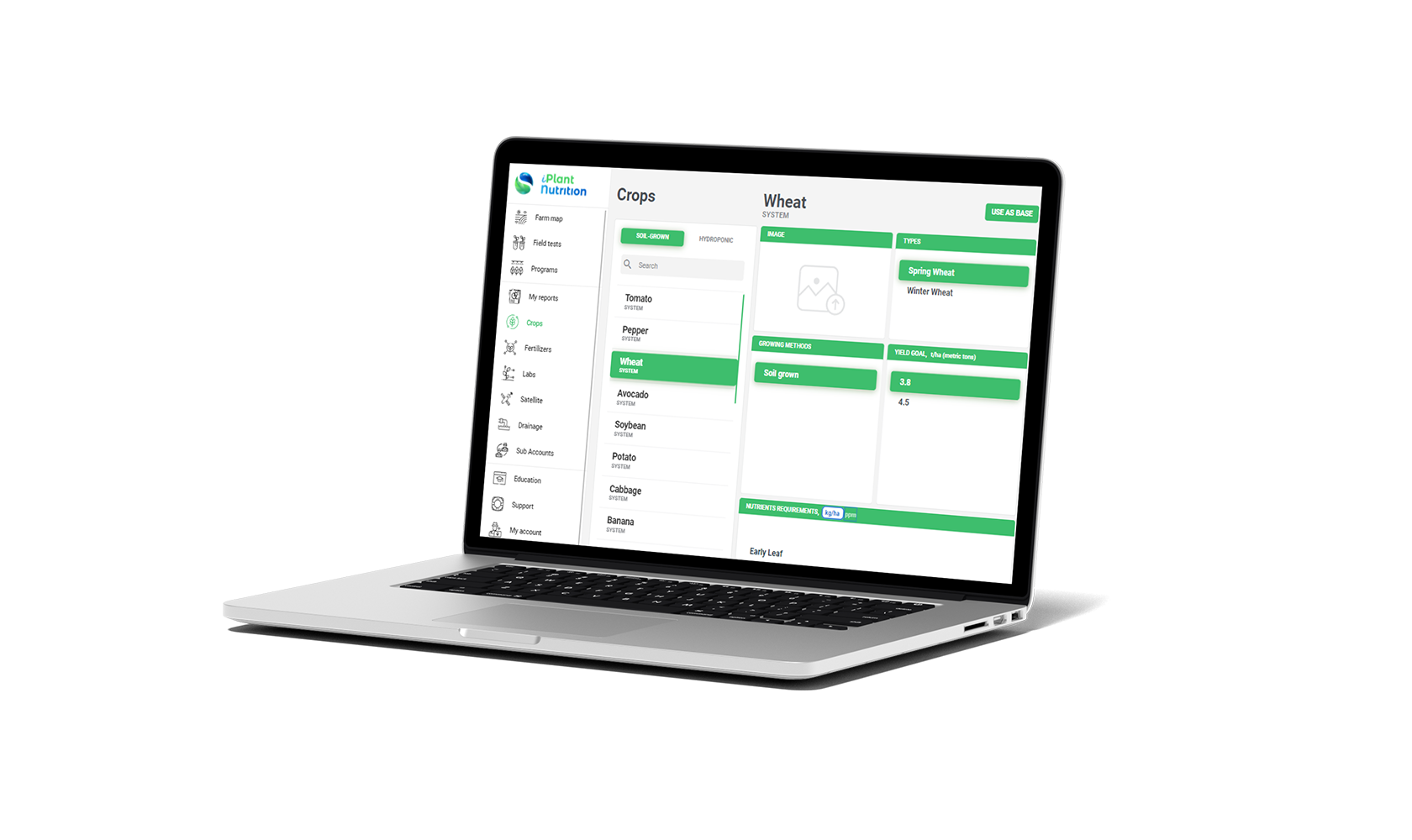 More Than 250 Crops
Choose Crop
More Than 250 Crops
Choose CropThat You Grow
 More Than 3000 Fertilizers
Select Fertilizers
More Than 3000 Fertilizers
Select Fertilizers& Cover Nutrients
 Detailed Report In PDF
Get Your Personal
Detailed Report In PDF
Get Your PersonalFertilization Plan





flower production with more
than 150 years of experience
in the flower market.
agriculture organization in Egypt,
advocating for climate change
and sustainability.
in precision agriculture,
included in TIME's “100 best
inventions of 2021” list.
for supporting and promoting
the AGRO sector in the
Domenica Republic.
 GroPlant
GroPlant
 YB Capital
YB Capital
 I-Feeder
I-Feeder
 YB Indoor Farm
YB Indoor Farm
 Plant Metrics
Plant Metrics
 YB Technologies
YB Technologies
 Yanmar
Yanmar
 YB AgTech
YB AgTech