Solarwinds Engineer39s Toolset V92 Serial Key Updated -
Back at her desk, Riya booted the laptop into its secure shell. The screen lit with a custom dashboard: network maps, alert streams, and an array of diagnostic utilities that could stitch together a tangled infrastructure like a surgeon closing a wound. The interface felt familiar and alien—designed by someone who loved systems the way a composer loves instruments.
When she closed the leather manual that morning, she found another note slipped inside, in handwriting she’d come to recognize across the toolkit’s margins: “Good night. We’re lucky to have you.” There was no signature.
Riya found the kit on a rain-slicked bench outside the data center, its case scuffed and warm from a recent touch. A faded sticker read Engineer39’s Toolset — V9.2 — the rest of the label peeled away as if someone had tried to hide what it was. solarwinds engineer39s toolset v92 serial key updated
One night, during a firmware upgrade, the network hiccupped and the upgrade rolled back across several racks. The monitoring stormed with alerts; fan speeds spiked; the UPS chimed. Riya felt the old dread—the kind that tightens your throat in the middle of a long shift. She pulled the braided tether, connected to the legacy controller, and used the toolset’s low-level probe to coax the failing boot loader. It took hours, patience, and a careful parity of reads. At dawn, as her eyes burned and the horizon outside the data center softened, the last server blinked to life and the network hummed steady.
But the kit had more than utilities. Tucked beneath the probes was a small printed photograph of a city skyline at dawn, with a note on the back: For the ones who keep the lights on. —M. Back at her desk, Riya booted the laptop
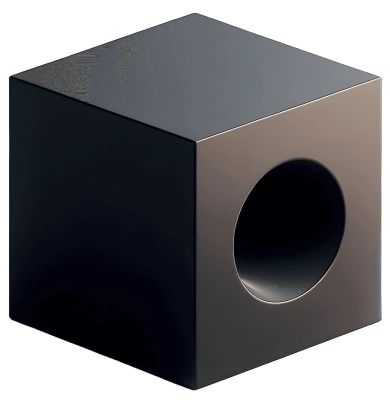
She hesitated, then opened it. Inside lay neatly organized tools: a compact laptop with an encrypted partition, a braided USB tether, a set of tiny serial probes, and a leather-bound manual filled with diagrams and handwritten notes. No serial keys, no activation prompts—only the quiet promise of capability.
Over the next week the toolset became her quiet partner. It exposed failing drives that had been masquerading as healthy, revealed a misconfigured SNMP trap that had left a black hole in monitoring, and even recovered a corrupted configuration file whose backup process had been silently failing for months. Each fix felt like returning a lost voice to the system. Riya left notes in the leather manual—timestamps, hypotheses, fixes—so the next engineer would know the system’s scars. When she closed the leather manual that morning,
At the rack she found a single ethernet cable half seated—an innocuous thing, but enough to confuse a controller into thinking its mirror had failed. She reseated it. The alerts faded. The dashboard’s health index climbed like dawn.